Independent Validation of Your Cybersecurity and Digital Resilience Status
Independent Assurance that your Cybersecurity Assessments Reflect Operational Reality
— NOT Just Reported Maturity.
Can We Trust Our Assessment Report?
Many organisations conduct cybersecurity maturity assessments or regulatory readiness reviews.
But boards increasingly ask one critical question:
How confident are we that the reported posture reflects reality?
Cyber Risk International’s Independent Validation Assessment provides objective, evidence-based verification of your cybersecurity or digital resilience assessment.

Get Started - Contact Us
Why Indepedent Validation Matters
Organisations face increasing expectations from:
-
regulators
-
boards of directors
-
internal audit
-
risk committees
to demonstrate that cybersecurity and digital resilience programmes are credible, evidenced, and effective.
However many assessments are:
-
internally performed
-
consultancy-led readiness reviews
-
self-declared maturity evaluations
Independent validation provides objective assurance that reported results are supported by evidence.
Assurance for Regulators
and Stakeholders

Assurance = Evidence

What Is an Independent Validation Assessment?
Independent Verification of Your Cybersecurity Assessment
An Independent Validation Assessment evaluates the accuracy and credibility of an existing cybersecurity or digital resilience assessment.
Rather than repeating the full assessment, Cyber Risk International performs a structured validation of previously reported results.
This includes:
Review of the original assessment or readiness report
Randomised control sampling
Evidence verification
Stakeholder interviews
Independent evaluation of findings
The outcome is a formal Validation Report designed for executive leadership and board oversight.
This approach provides assurance without repeating the full assessment exercise.
Validation Framework Lenses
Choose the Validation Lens That Matches Your Regulatory Environment
Independent Validation Assessments can be performed through the lens of major cybersecurity frameworks and regulatory regimes.
Supported Frameworks
NIST Cybersecurity Framework (CSF) 2.0
EU Digital Operational Resilience Act (DORA)
UK Operational Resilience Framework
ISO/IEC 27001
Central Bank of Ireland IT Risk Expectations (Credit Unions)
EU AI Act
NIS2 Directive
CyFun Cyber Fundamentals
Organisations select the framework through which validation will be performed.

Independent Validation Methodology
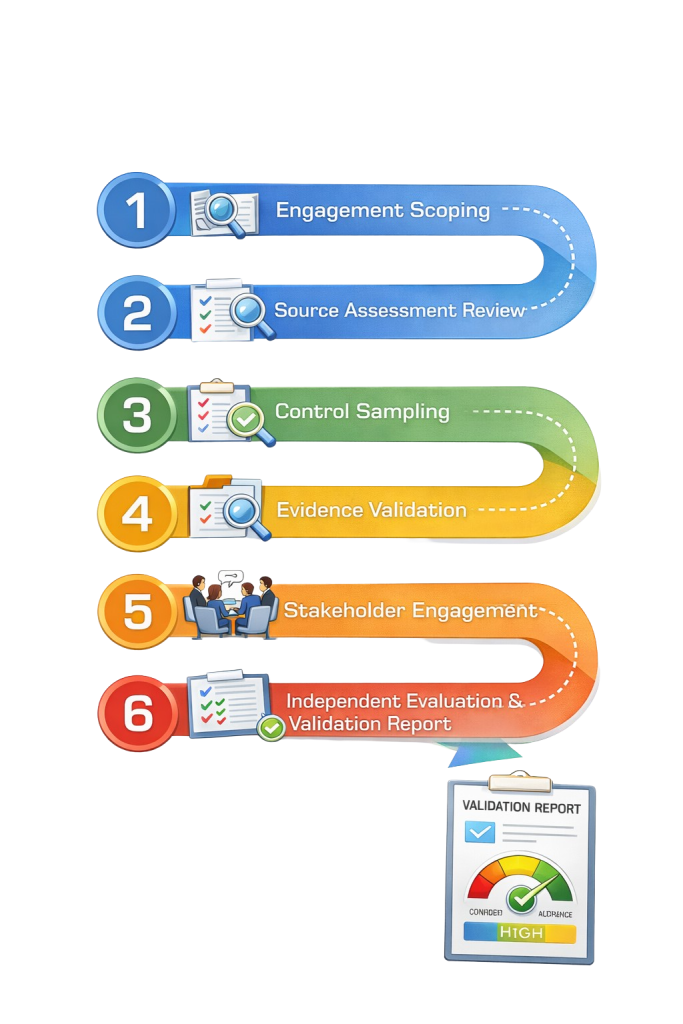
A Structured Evidence-Based Validation Process
Cyber Risk International applies a rigorous validation methodology supported by the CyberPrism Digital Resilience Platform.
Methodology Steps
1️⃣ Engagement Scoping
Define validation framework, organisational scope, and source assessment.
2️⃣ Source Assessment Review
Review the original assessment, maturity scoring, and reported control status.
3️⃣ Control Sampling
Select a randomised sample of controls or regulatory requirements.
4️⃣ Evidence Validation
Review policies, procedures, logs, governance documentation, and operational artefacts.
5️⃣ Stakeholder Engagement
Conduct sessions with relevant personnel to clarify control ownership and implementation.
6️⃣ Independent Evaluation & Validation Report
Produce a board-level report including findings and a Validation Confidence Rating.
This methodology builds an evidence-based picture of the organisation’s true cybersecurity posture.
Service Methodology Overview
Validation Confidence Rating
Board-Level Assurance Through a Validation Confidence Rating
Each Independent Validation Assessment includes a Validation Confidence Rating, indicating the degree to which evidence supports the reported cybersecurity posture.
| Rating | Meaning |
|---|---|
| High Confidence | Evidence strongly supports the reported cybersecurity posture |
| Moderate Confidence | Minor discrepancies identified but overall posture credible |
| Limited Confidence | Significant inconsistencies between reported posture and evidence |
| Low Confidence | Reported posture not supported by evidence |
This rating provides clear insight for boards and senior leadership.

Service Options
Validation Engagement Options
Standard Validation Assessment
Includes:
review of source assessment
randomised control sampling
evidence validation
stakeholder engagement sessions
Validation Confidence Rating
Executive Validation Report
Typical duration: 4–6 weeks
Deep Dive Validation Assessment
Includes:
expanded control sampling
deeper evidence analysis
additional stakeholder interviews
enhanced remediation guidance
Validation Confidence Rating
Board-level Validation Report
Typical duration: 6–8 weeks
Who This Service Is For
Independent Validation Assessments are ideal for organisations that:
want independent assurance for their board
are preparing for regulatory scrutiny
want to validate consultancy readiness reports
want assurance before ISO 27001 certification
are preparing for DORA or NIS2 compliance
want to strengthen cyber governance oversight
Validate Your Status with Confidence
Independent validation gives your board and regulators confidence that cybersecurity reporting reflects operational reality.
Board-Level Assurance Section
Independent Assurance for Leadership
The Independent Validation Assessment provides senior leadership with clear assurance regarding the credibility of the organisation’s cybersecurity posture.
Key Outputs
Independent Validation Report
Validation Confidence Rating
Identification of discrepancies
Strategic recommendations
This enables boards to determine whether management’s reported cybersecurity posture is supported by evidence and operational reality.
Digital Resilience with CRI
Cyber Risk International empowers organisations to achieve true digital resilience through expert-led advisory, integrated technology, and executive education — enabling leadership to confidently navigate complex threats and regulatory demands.

Cyber Risk International Ltd
ICTTF House – Unit 15, N17 Business Park, Tuam, Co Galway, H54 H1K2, Ireland
Registered Company: 550801 VAT: IE 3292853TH DUNS: 985605977
W: www.cri.ie E: [email protected] P: +353-(0)1-905 3260
Every organisation’s DORA obligations and risk profile are different.
Contact us to discuss how a DORA Validation Assessment can support your regulatory, audit, and board-level needs.
